Benutzer-Werkzeuge
gaeste-wlan
Dies ist eine alte Version des Dokuments!
Inhaltsverzeichnis
Freies Gäste-W-Lan
Information
Das Gäste-W-LAN steht Kunden kostenlos zur Verfügung. Die aktuelle Statistik lässt sich hier online aufrufen.
Das W-Lan wird über fast alle W-LAN Router bereitgestellt.
Installation am OpenWRT Router
WiFi Dog
Installation
opkg install wifidog dnsmasq /etc/init.d/wifidog enable /etc/init.d/dnsmasq enable
/etc/config/network
Ergänzen:
config interface 'g'
option type 'bridge'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '172.31.215.1'
/etc/config/wireless
Ergänzen:
config wifi-iface
option device radio0
option network g
option mode ap
option ssid PreunerWirt_FreeWiFi
option encryption none
option disabled 0
option isolate '1'
/etc/config/dhcp
Achtung: Falls der Router auch für das LAN einen DHCP Server bereitstellt muss die Sektion LAN konfiguriert werden!
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
config dhcp 'lan'
option interface 'lan'
option ignore '1'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config dhcp
option interface 'g'
option leasetime '12h'
option limit '252'
option start '2'
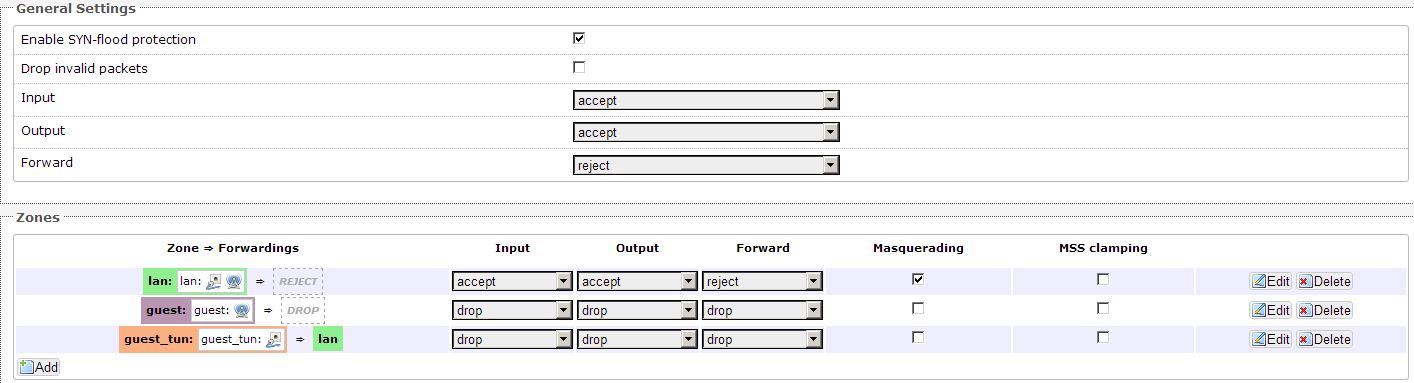
/etc/config/firewall
config defaults
option syn_flood 1
option input ACCEPT
option output ACCEPT
option forward REJECT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
option network 'lan'
option input ACCEPT
option output ACCEPT
option forward REJECT
option masq 1
config zone
option name wan
option network 'wan'
option input REJECT
option output ACCEPT
option forward REJECT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://dev.openwrt.org/ticket/10381
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option src_ip fe80::/10
option src_port 547
option dest_ip fe80::/10
option dest_port 546
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
# include a file with users custom iptables rules
config include
option path /etc/firewall.user
config zone
option name 'guest'
option output 'ACCEPT'
option network 'g'
option forward 'ACCEPT'
option input 'DROP'
config rule
option target 'ACCEPT'
option name 'DNS'
option src 'guest'
option dest_port '53'
config rule
option target 'ACCEPT'
option name 'DHCP'
option src 'guest'
option dest_port '67'
option proto 'udp'
config rule
option target 'ACCEPT'
option name 'WifiDog'
option src 'guest'
option dest_port '2060'
option proto 'tcp'
config rule
option target 'ACCEPT'
option name 'HTTP'
option src 'guest'
option dest_port '80'
option proto 'tcp'
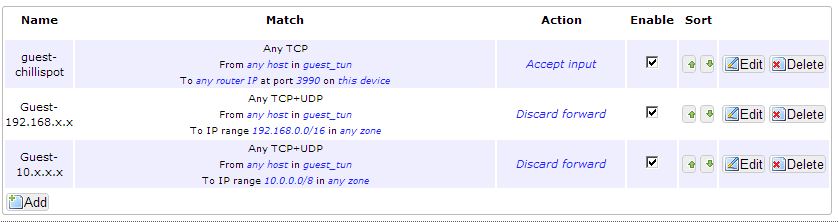
config rule
option name 'Guest-192.168.x.x'
option proto 'all'
option src 'guest_'
option dest_ip '192.168.0.0/16'
option target 'DROP'
option dest '*'
config rule
option name 'Guest-172.16x.x.x'
option proto 'all'
option src 'guest'
option target 'DROP'
option dest '*'
option dest_ip '172.16.0.0/12'
config rule
option name 'Guest-10.x.x.x'
option proto 'all'
option src 'guest'
option dest_ip '10.0.0.0/8'
option target 'DROP'
option dest '*'
config forwarding
option src 'guest'
option dest 'lan'
/etc/firewall.user
iptables -t nat -I PREROUTING -p udp --dport 53 -j DNAT --to-destination 8.8.8.8:53 iptables -t nat -I PREROUTING -i br-g -d 192.168.0.0/16 -j DROP iptables -t nat -I PREROUTING -i br-g -d 10.0.0.0/8 -j DROP /etc/init.d/wifidog restart
/etc/wifidog.conf
GatewayID ap-seiler
GatewayInterface br-g
HtmlMessageFile /etc/wifidog-msg.html
HTTPDUserName Uc2wee15lAaey14eiphopei
HTTPDPassword Im4aisahahxe123exaehae
AuthServer {
Hostname auth.smart-mt.at
Path /
}
ClientTimeout 5
FirewallRuleSet global {
FirewallRule block to 192.168.0.0/16
FirewallRule block to 172.16.0.0/12
FirewallRule block to 10.0.0.0/8
FirewallRule allow udp port 53
FirewallRule allow tcp port 53
FirewallRule allow udp port 67
}
FirewallRuleSet validating-users {
FirewallRule allow to 0.0.0.0/0
}
FirewallRuleSet known-users {
FirewallRule allow to 0.0.0.0/0
}
FirewallRuleSet unknown-users {
}
FirewallRuleSet locked-users {
FirewallRule block to 0.0.0.0/0
}
Konfiguration neu laden und starten
/etc/init.d/network restart /etc/init.d/firewall restart /etc/init.d/dnsmasq restart /etc/init.d/wifidog start
Coova-Chilli (veraltet)
Installation
# opkg update; opkg install coova-chilli
Chilli.conf
interval 3600 pidfile /var/run/chilli.pid radiusserver1 192.168.0.1 radiusserver2 192.168.0.1 radiussecret eNgai4peichuuk8Ainathooph8Ieza dhcpif br-guest uamserver http://www.smart-mt.at/chilli/login.php uamsecret shahliejuiju5ihahb4eg6eeX3Shaz uamallowed www.smart-mt.at,www.mblue.at uamanydns dns1 208.67.222.222 dns2 208.67.220.220 domain SmartMediaTechnology net 172.16.30.0/24 tundev tun1
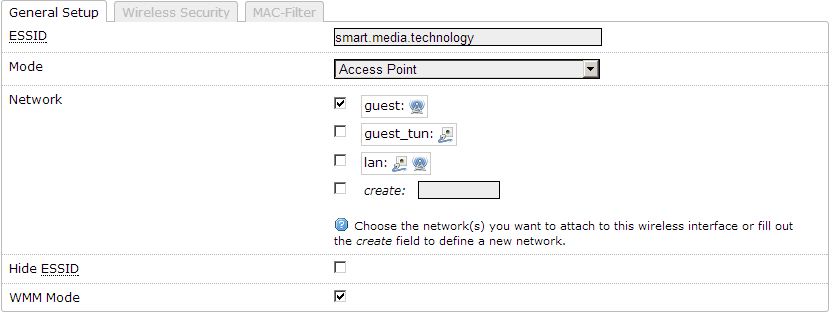
Wifi Settings
General Settings
Traffic Rules
gaeste-wlan.1417948845.txt.gz · Zuletzt geändert: 2014/12/07 10:40 von 192.168.0.12